Strengthening Microgrid Cybersecurity With Real-Time Simulation
Microgrid
02 / 20 / 2026

Key Takeaways
- Use real-time simulation and hardware in the loop to prove that cyber defenses preserve stable control and correct protection behavior under attack conditions.
- Prioritize controls that restrict and verify write actions across relays, controllers, and gateways, then confirm segmentation and inspection do not break timing requirements.
- Treat microgrid cybersecurity as an operating discipline with routine drills, patch validation against stress scenarios, and monitoring that ties network signals to physical outcomes.
Real-time microgrid simulation lets you prove cyber defenses before field risk.
Microgrid cybersecurity fails when teams treat controls, protection, and communications as separate workstreams instead of one coupled system. Reported losses from cybercrime reached $12.5 billion in 2023, and that pressure pushes leaders to ask for evidence, not assurances. Real-time simulation supplies that evidence because you can test how attacks shift power flows, trip logic, and operator visibility without putting people or assets at risk. The practical outcome is simple: you’ll spend less time debating hypotheticals and more time validating what stays safe under stress.
Microgrid attacks that target protection relays controllers and gateways

Attackers go after the devices that can change physical outcomes fast: protection relays, distributed energy resource controllers, the microgrid controller, and the gateways that bridge operational technology to enterprise networks. The risk is not only data loss. A small change to setpoints, time sync, or breaker control can push the system into unsafe operation, nuisance trips, or unstable islanding.
Start threat scoping with the write paths, not the read paths. Identify every interface that can alter relay settings, inverter modes, battery charge limits, breaker states, and load shedding priorities. Then trace how those commands travel through jump hosts, vendor remote access, cellular routers, protocol converters, and engineering workstations. Treat each conversion point as a place where authentication, integrity checks, and logging often weaken.
Microgrids amplify the impact of common control attacks because protection and control are already tuned near the edge of stability. Islanding transitions, black start sequences, and reconnection checks create moments where timing matters and margins shrink. Incident reports logged 290 industrial control system incidents in 2016, including 46 tied to the energy sector, which is a reminder that energy operations sit squarely on the target list. Your security plan has to assume an attacker will reach a control plane, then prove the system still behaves safely.
How real-time simulation improves detection triage and root cause
Real-time simulation improves detection because it gives you a controlled baseline where “normal” includes switching events, inverter transients, and protection actions. That baseline helps you separate a cyber event from a legitimate disturbance. It also improves triage because you can reproduce the sequence precisely, then validate which signal changed first and which control reacted.
Build your detection validation around time alignment. Pair electrical waveforms and controller internal states with network telemetry, then replay those conditions while you tune alarms and thresholds. Test the gap between what operators see on the human-machine interface and what the devices actually receive on the wire. When alarms fire too early or too late, you’ll see it as a measurable timing error, not a subjective debate.
Root cause gets easier when you can hold the grid conditions constant and vary only one factor at a time. A microgrid controller can look “compromised” when a weak voltage regulator is really the culprit, and a network spike can look “benign” when it masks a malicious setpoint write. Real-time execution matters because many failure chains only happen when latency, scan cycles, and device response times match what you run in operations. The output you want is a short list of detection rules you trust, plus a playbook that points engineers to the right logs first.
“Real time simulation supplies that evidence because you can test how attacks shift power flows, trip logic, and operator visibility without putting people or assets at risk.”
Define trust boundaries and data flows across distributed energy systems
Secure distributed energy systems start with clear trust boundaries, because the same microgrid often mixes utility-grade relays, building automation, cloud monitoring, and vendor maintenance channels. A boundary tells you where identity must be enforced and where commands must be constrained. Without that map, segmentation becomes guesswork and exceptions quietly turn into permanent backdoors.
Document data flows as verbs, not nouns. Focus on who can start and stop assets, who can change protection settings, who can approve an islanding transition, and who can push firmware. Separate monitoring from control so read-only traffic stays read-only all the way to the device, including through gateways and protocol bridges. Keep engineering access isolated from operator access so a compromised laptop cannot become an implicit control authority.
Trust boundaries should also reflect how work actually happens. Remote support, warranty service, and integration partners often need periodic access, and that need will not disappear after commissioning. Tight controls still fit if you treat access as a scheduled, logged session that expires, with approvals tied to a change ticket and device-level accountability. Microgrid simulation supports this work because you can test what segmentation and inspection do to timing, especially around protection messaging and controller scan rates.
Use hardware in the loop to test cyber physical defenses
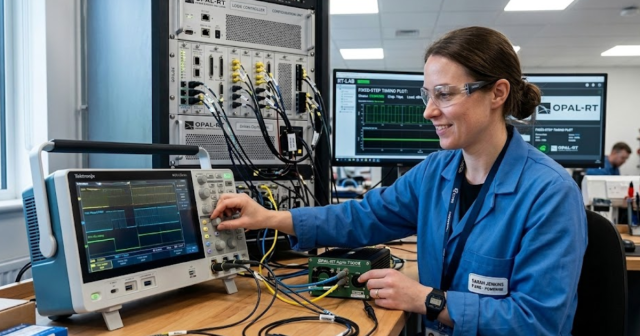
Hardware in the loop testing connects real controllers, relays, and communication gear to a real-time microgrid simulation so you can validate cyber defenses against physical consequences. That setup lets you test the full chain from network traffic to actuator commands to electrical response. The key value is fidelity under timing pressure, since many unsafe outcomes depend on milliseconds and control cycles.
A concrete test looks like this: a campus microgrid controller and feeder relay are wired into a simulator that models a battery inverter, photovoltaic generation, and a critical load block. A malicious command is injected that shifts frequency reference and suppresses an alarm bit at the same time, which forces the controller to chase a false condition while operators see “green” status. The pass criteria is not only that alarms appear, but that droop control stays stable, relay trips remain selective, and the system returns to a safe operating state with a verified audit trail.
Execution discipline matters more than tool choice, but the tooling has to support deterministic behaviour and detailed capture. OPAL-RT platforms are often used here because they can run power system models in real time while interfacing with protection and control hardware over the same kinds of I/O and protocols you use in a lab. The goal is repeatable evidence: the same injected condition should yield the same control response, and changes to defenses should produce measurable improvements.
|
Security question you must answer |
Evidence that proves you answered it |
| A compromised setpoint cannot exceed safe operating limits. | Recorded controller outputs show enforced bounds under attack. |
| Protection still clears faults without unsafe overtrips. | Time-stamped relay events confirm selectivity and coordination. |
| Operators see truthful status during comms manipulation. | HMI screens and device states match in synchronized logs. |
| Segmentation does not break control timing requirements. | Measured latency stays within the controller scan budget. |
| Incident response steps work under operational load. | Runbooks complete within target times during drill playback. |
Controls to prioritize for secure operation without grid instability
Security controls for microgrids have to reduce attack impact without breaking protection performance or control stability. Prioritization should focus on shrinking who can write, what they can write, and how quickly you can detect and reverse an unsafe change. The best controls are the ones that hold up during islanding, fault clearing, and reconnection when timing and availability matter most.
- Require multifactor authentication for every remote session into OT access points.
- Use strict role-based access so only named roles can write settings.
- Segment protection, control, and monitoring networks with explicit allow rules.
- Log every setpoint write and configuration change with time sync checks.
- Design a safe fallback mode that preserves protection and minimum load service.
“The practical judgment is straightforward: microgrid cybersecurity is a performance problem, not a policy problem.”
Tradeoffs show up quickly once you measure latency and operational burden. Deep packet inspection and aggressive network filtering can introduce delay or jitter that protection schemes will not tolerate, so you should validate the impact on relay messaging and controller scan cycles. Strong authentication can also fail operationally if it blocks urgent maintenance during an outage, so build emergency access procedures that still leave an auditable trail. The priority is not “maximum security,” it is stable control with bounded risk.
Simulation failure modes that lead to false security confidence
Simulation can mislead when it hides the same constraints that make attacks dangerous in operations: timing, noise, device quirks, and human response. False confidence happens when models behave ideally, communications never drop, and controllers never hit edge cases. The fix is not more complexity, but tighter alignment between what you simulate and what you actually run.
Watch for gaps that quietly remove the attacker’s advantage. Perfect time synchronization, unrealistically clean measurements, and network links with constant latency will mask failures that appear during islanding transitions and switching events. Device behaviour can also be oversimplified when firmware-dependent limits, retries, and lockouts are not represented. Operator workflow matters too, since the time it takes to notice, verify, and act often determines the physical outcome.
Guardrails keep the work honest. Validate models against recorded operational data, then run sensitivity checks that sweep timing, load levels, and comms delay across realistic ranges. Require pass criteria that include physical metrics, not only security metrics, so a defense that prevents a write but causes nuisance trips still fails. Bring protection engineers, controls engineers, and security staff into the same acceptance review so each discipline can challenge assumptions that others miss.
Run monitoring patching and response drills using simulated incidents

Security readiness improves when monitoring, patching, and response drills are treated as operational tests that must pass, not documents that must exist. Simulated incidents let you rehearse actions under the same timing pressure you face during an outage or fault. That practice builds confidence because teams learn what signals to trust and what steps restore safe control fastest.
Make drills routine and scoped. Validate a patch or configuration change against the scenarios you care about most, then roll it forward only after the control system response remains stable and the alarms still point to the right cause. Use the same logging and alerting stack you run day to day so every test also hardens your monitoring pipeline. Capture outcomes as measurements, including response time to isolate affected segments and time to restore verified setpoints.
The practical judgment is straightforward: microgrid cybersecurity is a performance problem, not a policy problem. Teams that treat microgrid simulation as an acceptance gate catch unsafe interactions early, and they stop debating security in the abstract because the system either passes or it does not. OPAL-RT fits into that pattern when you need repeatable real-time tests that connect controls and protection to physical behaviour under stress. Tight execution, clear pass criteria, and regular drills will do more for secure distributed energy systems than any one-time assessment.
EXata CPS has been specifically designed for real-time performance to allow studies of cyberattacks on power systems through the Communication Network layer of any size and connecting to any number of equipment for HIL and PHIL simulations. This is a discrete event simulation toolkit that considers all the inherent physics-based properties that will affect how the network (either wired or wireless) behaves.