Building Cybersecurity Simulation Training For Utilities
Industry applications
02 / 24 / 2026

Key Takeaways
- Utility cybersecurity simulation training improves readiness when it tests operational choices under pressure, not just technical knowledge.
- A repeatable cyber range program depends on disciplined building blocks that connect scenarios, assets, tools, roles, and safety rules into one system.
- Measured improvement comes from closing the loop after each exercise with owned fixes to playbooks, configurations, and escalation paths.
Utilities can’t treat cybersecurity as a paperwork exercise, because your worst day includes operators, engineers, vendors, and executives trying to make safe calls under time pressure. Simulation training gives everyone the same pressure, the same tool friction, and the same communication gaps you’ll face during an incident. You find weak handoffs early. You fix them before a control room is flooded with bad alerts.
Done well, utility cybersecurity training builds muscle memory across IT and OT while keeping work safe and repeatable. You learn which detections matter, which steps waste time, and which approvals block containment. Teams also get practice writing clear updates for leadership and external parties. That’s how readiness becomes measurable, not assumed.
“Simulation-based cyber training lets utility teams rehearse incidents without putting service at risk.”
Cybersecurity simulation training for utilities and what it covers

Cybersecurity simulation training is structured practice where your team responds to a staged cyber event using your playbooks, tools, and communications. It tests people, process, and technology as a single system. A cyber range simulation adds a controlled technical setup that can mimic parts of your network. Utilities use it to rehearse actions without touching production systems.
Utility teams get the most value when the training forces tradeoffs, not trivia. That means practicing triage, containment, recovery, and reporting with the same constraints you’ll face during a shift. The output is not a certificate. The output is a short list of changes to playbooks, access rules, alert tuning, backups, and escalation paths.
Readiness goals and constraints for utility OT and IT teams
Cyber readiness for utilities means keeping operations safe while restoring visibility and control quickly. OT constraints shape every choice, since availability and safety interlocks matter more than perfect forensics. IT constraints still matter, since email, identity, and remote access often sit on the attack path. Training has to cover both domains without forcing unsafe testing on live control systems.
Set goals your teams can act on, such as time to recognize an OT-impacting event, time to isolate a remote access route, and time to brief operations leadership with clear options. Keep constraints explicit: maintenance windows, vendor support hours, change control rules, and unionized roles. That clarity keeps exercises focused and prevents “hero” behaviour that won’t work during actual incidents.
8 building blocks for a utility cyber range program
A useful cyber range program is built from repeatable parts that you can run, score, and improve over time. Each block ties training to operational risk, not abstract threats. The goal is consistent practice under controlled conditions. Teams leave with fixes they can schedule and verify. That’s how cybersecurity simulation training improves readiness instead of just raising awareness.
1. Pick high-impact scenarios tied to outage and safety risk
Start with scenarios that force operational choices, not just technical tasks. Link each scenario to a service impact you can explain to operations leadership. One exercise might stage ransomware in the billing network that also disables a jump server used for OT engineering access, forcing a choice between isolation and restoration. Keep scope tight so the team can finish a full cycle from detection to recovery. Record what slowed containment.
2. Map critical assets and trust zones across IT and OT
Create a simple map that shows where data and access cross boundaries, especially remote access, historian flows, and vendor paths. Treat zones as training “rooms” so participants can describe where they are acting and why. Align asset labels to what your teams use in tickets and runbooks. Add clear ownership for each zone so escalations are fast. Update the map after each exercise, not once a year.
3. Build an attack path library using threat intelligence
Turn threat reports into a short library of steps an attacker would take in your setup. Focus on identity abuse, remote access misuse, and lateral movement into OT support systems. Each path should state the prerequisite access and the likely detection points. Keep the library small enough that teams can memorize the common patterns. Refresh it when your architecture changes or new access methods appear.
4. Choose the right fidelity from tabletop to cyber range
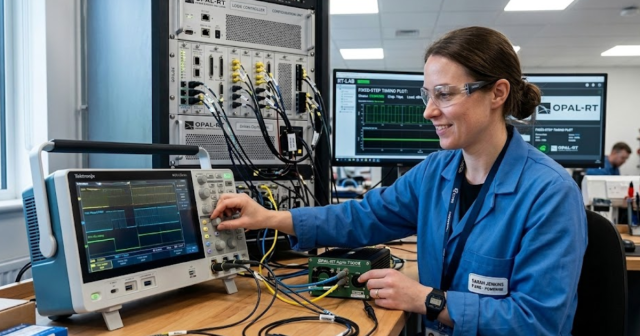
Match fidelity to what you need to validate. Tabletop work is best for communication, authority, and escalation timing. A lab setup helps validate tooling, logging, and operator workflows. Some teams use a real-time digital simulator such as OPAL-RT to pair control logic behavior with cyber event injects without touching production equipment. The best choice is the one that tests your riskiest assumptions safely.
5. Integrate tools for detection logging forensics and response actions
Training fails when teams practice on tools they will not use during incidents. Pull in your SIEM views, alert queues, ticketing, call trees, and remote access controls. Make sure the range can generate logs that look like your actual telemetry, even if volume is smaller. Include a clean way to capture actions and timestamps. That gives you evidence to tune alerts and tighten containment steps.
6. Assign roles and communication flows for incident command

Define roles before the exercise starts, then enforce them during play. Cover incident commander, operations liaison, IT lead, OT lead, legal and regulatory contact, and vendor manager. Make each role responsible for a specific set of decisions and updates. Use short update cycles so leadership hears consistent status, not conflicting details. Practice writing a one-paragraph situation report that states impact, actions, and next steps.
7. Design injects scoring and stopping rules for safe training
Injects should force decisions that expose gaps, not surprise people with impossible tasks. Scoring should reward early isolation of risky paths, clear communications, and correct prioritization of safety. Stopping rules matter just as much, since OT practice must stay safe and controlled. Define what ends the exercise, such as loss of safe control, a simulated safety trip, or a time cap. Those rules prevent overreach and keep learning consistent.
8. Turn lessons into updated playbooks configs and controls
Convert exercise notes into work items with owners and due dates. Update playbooks in the same system you use for operations procedures so they don’t drift. Treat logging and detection changes as configuration work with review, not ad hoc tweaks. Re-run the same scenario after changes so you can prove improvement. Close the loop with a short readout that states what changed and how it will be validated.
| Building block | What success looks like |
| Pick high-impact scenarios tied to outage and safety risk | The scenario forces clear operational choices under time pressure. |
| Map critical assets and trust zones across IT and OT | Teams share the same map and use it during escalation. |
| Build an attack path library using threat intelligence | Defenders recognize common sequences and check the right signals. |
| Choose the right fidelity from tabletop to cyber range | The exercise tests risky assumptions without touching production systems. |
| Integrate tools for detection logging forensics and response actions | Participants work inside their normal tools and capture timestamps. |
| Assign roles and communication flows for incident command | Updates stay consistent because owners and paths are pre-set. |
| Design injects scoring and stopping rules for safe training | Play stays controlled and results can be compared across runs. |
| Turn lessons into updated playbooks configs and controls | Fixes become owned tasks and get verified in the next run. |
“Pick the lightest option that still tests your biggest unknowns, then expand fidelity only when the gaps demand it.”
Running exercises and measuring improvements across people process technology
Run exercises on a cadence you can support, then measure what changed across staffing, procedures, and tooling. Track time to identify the likely entry point, time to isolate remote access, and time to provide a usable status update to operations leaders. Measure rework, such as reversed actions or conflicting tickets. Use the same metrics each run so progress is obvious.
Keep facilitation strict so the team learns from friction instead of arguing about rules. Log decisions, approvals, and handoffs, since those steps usually dominate response time. Treat false alarms as a training input, not a distraction, because alert overload is a readiness problem. After-action work should fit into normal change control so fixes actually land.
Choosing simulation types and vendors for utility risk reduction
The main difference between tabletop exercises and cyber range simulation is what you can verify with evidence. Tabletop work validates communication, authority, and playbook clarity. A cyber range validates tool behaviour, logging, access controls, and technical steps under stress. Pick the lightest option that still tests your biggest unknowns, then expand fidelity only when the gaps demand it.
Use a short selection checklist: range isolation, OT safety controls, ability to replay scenarios, support for your log sources, and a clear method to score outcomes. Vendor lock-in is a risk if your team can’t adapt scenarios as systems change. OPAL-RT is one option teams use when they need real-time simulation tied to power system behaviour, but the right choice always depends on what you need to validate next. The strongest programs stay focused on repeatable practice and verified fixes.
EXata CPS has been specifically designed for real-time performance to allow studies of cyberattacks on power systems through the Communication Network layer of any size and connecting to any number of equipment for HIL and PHIL simulations. This is a discrete event simulation toolkit that considers all the inherent physics-based properties that will affect how the network (either wired or wireless) behaves.