6 Ways grid resilience testing strengthens energy security
Simulation, Energy
12 / 30 / 2025

Key Takeaways
- Grid resilience testing ties cybersecurity work to measurable service outcomes.
- Repeatable scenarios expose weak paths, operator gaps, and protection risks that cause outages.
- Retest discipline turns findings into security work your teams will execute.
Grid resilience testing makes energy security measurable. It shows how your grid behaves when cyber incidents and faults collide. Paper controls won’t show that.
Grid resilience testing shows why it matters for cybersecurity and how grid testing improves energy security. It highlights service gaps you will fix and retest.
Why grid resilience testing matters for modern energy security
Grid resilience testing links cybersecurity work to power delivery outcomes you will measure. It checks how technology, procedures, and people perform. The output is a scored list of gaps tied to visibility loss, unsafe switching, or longer restoration.
A storm scenario where remote access is abused and telemetry freezes will expose weak points. Operators will practice switching to alternate status checks, isolating a suspect link, and running in a degraded mode.
Engineers will see which controls fail first, such as shared accounts or weak separation. Fixes become obvious because the test shows what broke. That clarity speeds fixes and retests.
“Isolation and restoration times become team-owned targets.”
6 ways grid resilience testing strengthens energy security

1. Identifies grid cyber weaknesses before attackers exploit them
Grid cyber resilience starts with knowing the easiest path to high-impact assets. Resilience tests validate access control, identity, and segmentation as they actually work, not as they’re documented. The output is a short list of weak paths ranked by service impact. Focus on paths to setpoints, firmware, or switching authority.
A credential misuse scenario that reaches a substation engineering workstation will show if privilege boundaries are real. If the same account has rights to change relay settings and device firmware, that path will become your top fix. Tightening remote access rules, removing shared accounts, and improving logging will close it. Retesting the same path confirms the weakness is gone and the risk fell.
2. Validates operator response under coordinated cyber incidents
Cybersecurity on the grid includes human response, not just controls. Testing checks if the control room, IT security, and field crews act in the right order under pressure. It measures alarm handling, escalation, and authority to isolate systems without causing extra outages. Isolation and restoration times become team-owned targets. Manual fallback steps get rehearsed and timed.
A drill that mixes malware alerts with loss of feeder visibility forces hard calls. Dispatch will switch to local control, verify breaker status via alternate channels, and maintain limits. The drill will expose gaps such as a blocked remote access route no one told dispatch about. Updating runbooks and repeating the drill will turn response into a reliable workflow.
3. Exposes cascading failure paths across linked grid assets
Service loss spreads through shared dependencies more than single device failure. Resilience testing maps how faults propagate across control centers, substations, telecom links, and shared authentication services. It identifies common points that will take down many sites if they fail. Watch shared time sources and remote access hubs.
A test that breaks time sync while flooding control traffic will still allow protection to operate, yet event records become unreliable. Another chain appears when a patch disrupts a shared tunnel used for outage tools and substation access. Seeing the chain on a timeline makes it easier to defend redundancy and segmentation choices. The end result is fewer surprise couplings and a smaller blast radius.
4. Confirms protection system behavior during abnormal grid states
Protection logic expects physical faults, yet cyber events will trigger the same trips when data or setpoints are corrupted. Resilience testing checks relay timing, coordination, and automation behavior during abnormal grid states. It proves that settings remain safe when measurements and comms degrade. Fail-safe defaults get tested, not assumed.
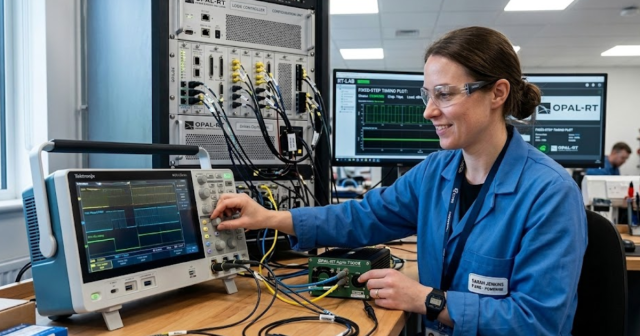
A bench test that replays a fault with tampered current values will show if a relay trips too fast. Teams using OPAL-RT connect physical protection devices to a real-time simulator and compare trip timing to expected coordination. If a spoofed value causes misoperation, you’ll catch it early and adjust thresholds or add sanity checks. Retesting confirms the change protects stability without masking real faults.
5. Measures recovery time after cyber and operational disruptions
Energy security improves when restoration is timed and rehearsed. Grid resilience testing measures how quickly monitoring, dispatch tools, and field communications can be restored after a disruption. It also reveals hidden dependencies, such as identity services, certificates, and spare hardware. Each dependency gets an owner and a restore step.
A restoration run that starts with a wiped workstation and an unavailable historian will force teams to rebuild and validate trust. The clock will expose bottlenecks like missing admin credentials, stale backups, or undocumented firewall rules. Fixing those gaps will cut recovery time for ransomware events and for routine failures like bad updates. Repeating the run gives you a real recovery target to track.
“Small verified gains will beat big plans that never get retested.”
6. Prioritizes grid investments based on tested risk exposure
Security budgets are limited, so work needs a tested order. Resilience testing ranks findings by service impact, ease of compromise, and recovery cost. It separates low-cost configuration fixes from changes that require capital or outages. The ranking will justify needed maintenance windows. Priority stays tied to tested service impact.
A test will show if remote access is the fastest route to high-impact changes while physical controls are strong. That evidence supports spending first on segmentation, multi-factor access, and hardened jump hosts, before adding new sensors. Another test will show a second communications path cuts restoration time more than any alert rule. Each choice ties to measured outcomes, so your plan holds up over time.
| Identifies grid cyber weaknesses before attackers exploit them | Testing finds weak paths so you fix them first. |
| Validates operator response under coordinated cyber incidents | Drills prove containment without harming service. |
| Exposes cascading failure paths across linked grid assets | Dependency maps reveal points so failures stop spreading. |
| Confirms protection system behavior during abnormal grid states | Replay tests confirm that protection remains safe with incorrect data. |
| Measures recovery time after cyber and operational disruptions | Restorations expose bottlenecks, keeping targets realistic. |
| Prioritizes grid investments based on tested risk exposure | Tested rankings guide spending to best reliability payoff. |
Applying grid resilience testing results to security planning

Testing results matter only when they become work you’ll complete and retest. Assign each finding an owner and deadline, tied to restoration time or loss of visibility. Keep the feedback loop short so each retest confirms progress.
Start with a scenario that already caused outages and turn lessons into tracked changes. Labs that run replayable scenarios on real-time simulators like OPAL-RT will keep a small library of faults, comms losses, and bad telemetry. That library keeps fixes honest after network changes or relay setting updates.
- Assign owners and review fixes weekly
- Set pass-fail metrics tied to customer minutes and safety limits
- Retest each scenario and record the score
- Update runbooks and train crews
- Report results tied to service continuity
Treat testing as routine work. Run the same hard scenarios after every major change. Small verified gains will beat big plans that never get retested.
EXata CPS has been specifically designed for real-time performance to allow studies of cyberattacks on power systems through the Communication Network layer of any size and connecting to any number of equipment for HIL and PHIL simulations. This is a discrete event simulation toolkit that considers all the inherent physics-based properties that will affect how the network (either wired or wireless) behaves.