How cyber attack simulations improve grid reliability
Simulation, Microgrid
12 / 18 / 2025

Key Takeaways
- Treat cyber attack simulation like reliability testing with defined failure modes, repeatable inputs, and measured recovery time.
- Prioritize scenarios that can change setpoints, protection behavior, or operator visibility, then retest after each control change.
- Investments pay off when simulations validate technical controls and operator procedures under realistic timing limits.
Cyber attack simulations improve grid reliability when you treat cyber risk like an engineering test with repeatable inputs and measured outputs. Power outages are estimated to cost the U.S. economy $150 billion annually. That cost makes “good enough” security a reliability problem, not only an IT concern. Controlled simulations let you learn how attacks affect operations without risking customer outages.
A useful cybersecurity simulation focuses on what operators and automation will do under stress. The model needs power system behavior, control paths, and the human handoffs that keep the system stable. You will get better results when cyber attack simulation runs are tied to specific failure modes and restoration steps. That’s the link between cyber resilience testing and day to day reliability.
Cyber attack simulations provide a direct test of grid failure modes
Cyber attack simulation strengthens reliability because it turns an abstract threat into a specific operational failure mode. The output is a clear answer to what breaks first and how fast it breaks. The test also shows what stays stable when controls work as designed. Those observations beat a long list of vulnerabilities with no operational context.
A scenario that maps cleanly to reliability starts with a compromised operator account that changes a voltage setpoint on a substation regulator. Voltage rises, capacitor banks switch more often, and feeder losses climb while alarms compete for attention. A second run injects false measurements so the control room trend looks normal while the feeder drifts out of limits. Operators then have to decide when to move to manual control and what checks to trust.
That kind of simulation of cyber attacks matters because grid failures rarely look like a single clean event. Small control errors can build into thermal overloads, low voltage pockets, and nuisance trips. The simulation will reveal which alarms matter, which ones distract, and where procedures need clearer triggers. Reliability improves when those triggers get practiced and refined.
“Those observations beat a long list of vulnerabilities with no operational context.”
Simulation of cyber attacks exposes control system and protection gaps
Simulation of cyber attacks surfaces gaps where control logic and protection logic assume trusted inputs. Many OT systems accept commands and settings changes that look valid on the wire. Protection schemes also assume disturbances follow physics, not adversary timing. A cybersecurity simulation will show how those assumptions fail under realistic access paths.
A common example starts with an attacker reaching an engineering workstation used for relay settings. A small pickup change can cause nuisance trips during load swings, or delay clearing during a fault. Another scenario delays protection signals so interlocking steps occur out of order during a switching sequence. The outcome looks like a coordination problem, yet the root cause is a cyber path into settings and timing.
The reliability lesson is not “add more security tools.” The lesson is to harden the few places where a settings change or message delay can cause a protection misoperation. Simulations are also a fast way to spot hidden dependencies such as time sync, vendor remote access, and shared service accounts. Fixing those weak points reduces both cyber exposure and avoidable trips.
Cyber resilience testing measures response speed and recovery limits

Cyber resilience testing improves reliability when it measures how long you operate with reduced visibility and reduced control. Response speed matters because the grid keeps moving while teams investigate. Recovery has stages, since you must restore trusted telemetry before major switching. A good test produces time based metrics you can compare run to run.
A practical drill starts with a loss of the primary HMI while field devices keep regulating voltage and frequency. Operators shift to local panels and phone confirmations while the cyber team isolates a suspected jump host. Dispatch then runs in a conservative mode because measurement trust is lower. Three Cyber Security Incident reports were received in 2023 under CIP-008-6 reporting, down from eight in 2022.
The most useful measures include time to detect abnormal control commands, time to isolate the affected segment, and time to restore known good configurations. A clean baseline run helps you separate cyber effects from normal control noise. Repeat the same scenario after a playbook update, then compare the timing. Faster, calmer recovery is a reliability outcome you can validate.
Grid reliability improves when simulations guide testing priorities
Grid reliability improves when you prioritize cyber attack simulation runs that can cause the largest operational swings. A huge catalog of possible attacks will waste lab time and attention. Strong prioritization links each scenario to a clear electrical impact and an actionable fix. That keeps cyber resilience testing focused on reliability outcomes.
Use these filters to choose scenarios that will move the needle:
- Pick actions that can change setpoints, trip logic, or switching authority.
- Focus on assets with shared access paths such as jump hosts.
- Target links that carry protection signals, interlocks, or dispatch data.
- Include a scenario that forces manual operation under limited visibility.
- Tie each scenario to a control change you will retest after hardening.
A high value sequence starts with compromised access that feeds bad load data into an automated dispatch routine. The first run shows how voltage violations spread when controls chase bad inputs. The second run tests tightened access plus sanity checks on incoming telemetry. That structure turns simulations into an engineering backlog, not a one time event.
High fidelity cybersecurity simulation supports safer grid validation
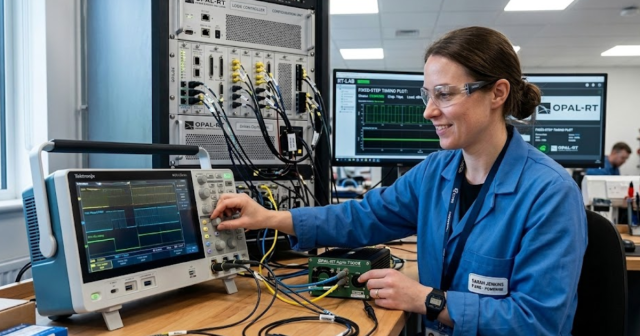
High fidelity cybersecurity simulation improves reliability because it preserves control loop timing and protection behavior. Tabletop exercises help coordination, yet they will not show how small delays change relay responses. A lab setup lets you run simulation of cyber attacks against realistic controllers without risking customer service. Closed loop testing exposes stability issues that network tests miss.
| Simulation style | What it clarifies for reliability |
| Tabletop exercise | It tests escalation and isolation speed. |
| OT network emulation | It shows how delay and replay affect control traffic. |
| Closed loop software simulation | It shows how false data pushes unstable control actions. |
| Hardware in the loop testing | It shows how real relays respond under cyber stress. |
| Restore drill with backups | It shows how long rebuild and validation actually take. |
A feeder model paired with a relay is a practical starting point. Delay and false data can be injected during switching. OPAL-RT real-time digital simulators keep the power system model synchronized with controller hardware, so timing stays honest. Lab access and data handling need strict rules. Setup effort rises, but uncertainty drops.
Common gaps limit the value of cyber attack simulation results

Cyber attack simulation falls short when it skips realistic access paths or ignores operator workload. Many tests assume the attacker already controls the relay, which hides the pathway you need to defend. Others focus on network blocks and miss configuration and time sync weaknesses. Those gaps create false confidence, and false confidence will harm reliability.
A familiar miss looks like this: the test models a firewall block, then celebrates, yet the attacker route is a maintenance laptop plugged into a service switch. Another miss blames a single relay for a misoperation when time drift across devices is the real trigger. A third miss ends the run after containment and never validates restore steps, so corrupted settings return later. Each issue becomes visible once the simulation includes access, timing, and restoration.
Better cyber resilience testing sets clear attacker limits, operator limits, and stop rules before the run starts. Each run also needs an after action change, not just a report. Retest after changes, then keep the scenario in rotation. That loop is how simulations stop being theater and start improving reliability.
“Simulation outcomes will improve grid reliability only when results change what you build, train, and maintain.”
Simulation outcomes inform investment and operational readiness choices
Simulation outcomes will improve grid reliability only when results change what you build, train, and maintain. The most useful output is a ranked set of failure modes tied to concrete controls and repeatable retests. Some fixes belong in technology, such as tighter control over settings changes and stronger validation of telemetry. Other fixes belong in operations, such as manual switching practice when visibility drops.
A practical funding choice often comes down to reducing impact, not chasing every intrusion path. Segmentation that limits lateral movement will shrink the affected area when a workstation is compromised. Offline backups with routine restore drills will cut downtime when systems need rebuild. Training that repeats the same simulated disturbance will build calm habits for operators and responders. OPAL-RT lab setups can support this repeatability when controller hardware needs to be in the loop for timing limits.
Reliability comes from disciplined execution. Simulations matter only when you keep them scoped, measured, and repeatable after each material change. That discipline will turn cyber events into manageable disturbances instead of service interruptions. Teams that treat each run as a reliability test will keep improving long after the first exercise ends.
EXata CPS has been specifically designed for real-time performance to allow studies of cyberattacks on power systems through the Communication Network layer of any size and connecting to any number of equipment for HIL and PHIL simulations. This is a discrete event simulation toolkit that considers all the inherent physics-based properties that will affect how the network (either wired or wireless) behaves.